Cybersecurity Act
Cybersecurity Directive
Security measures for information security
Environmental Management System
General Data Protection Regulation
Regulation of the European Parliament and of the Council on Artificial Intelligence
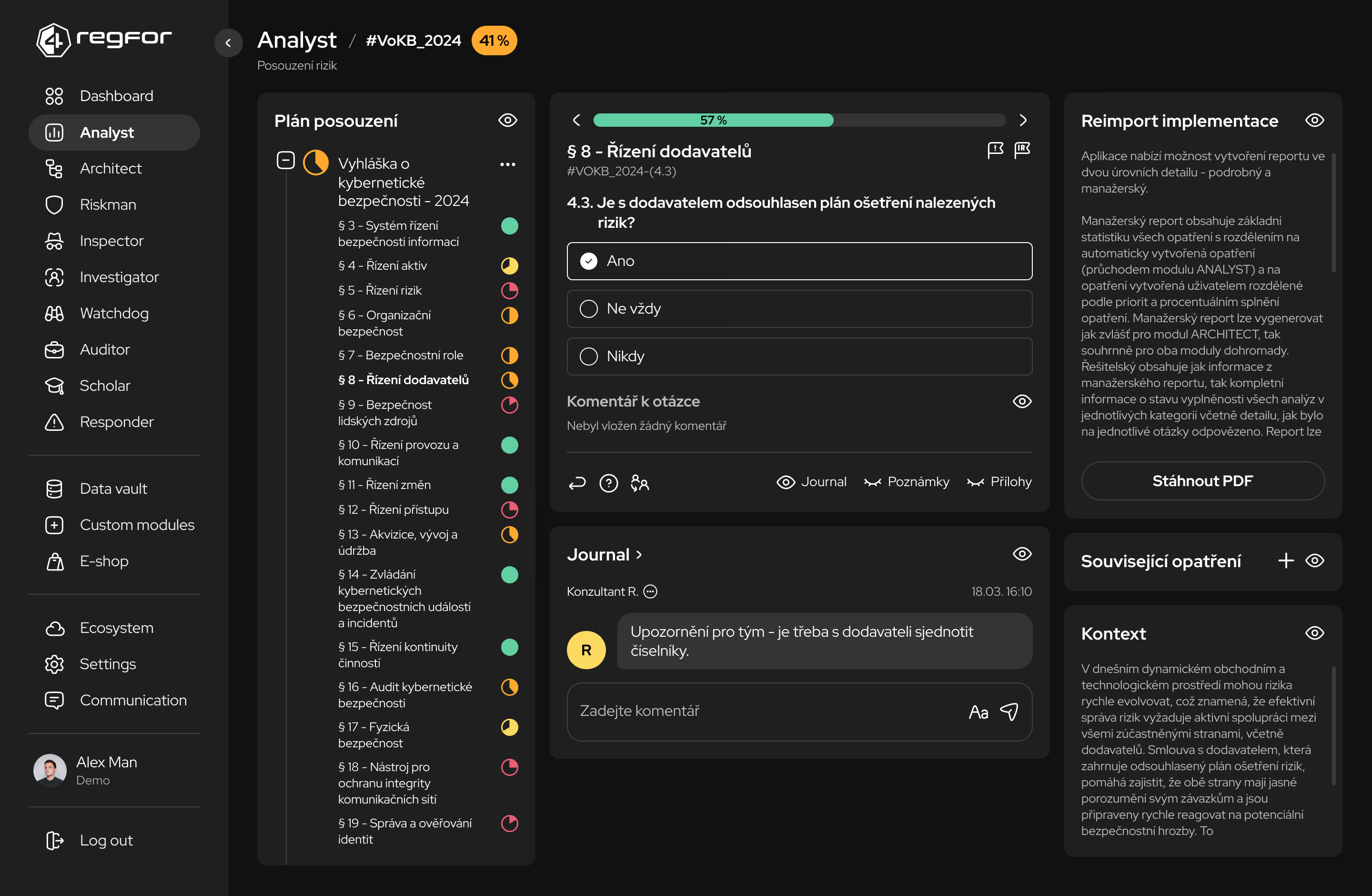
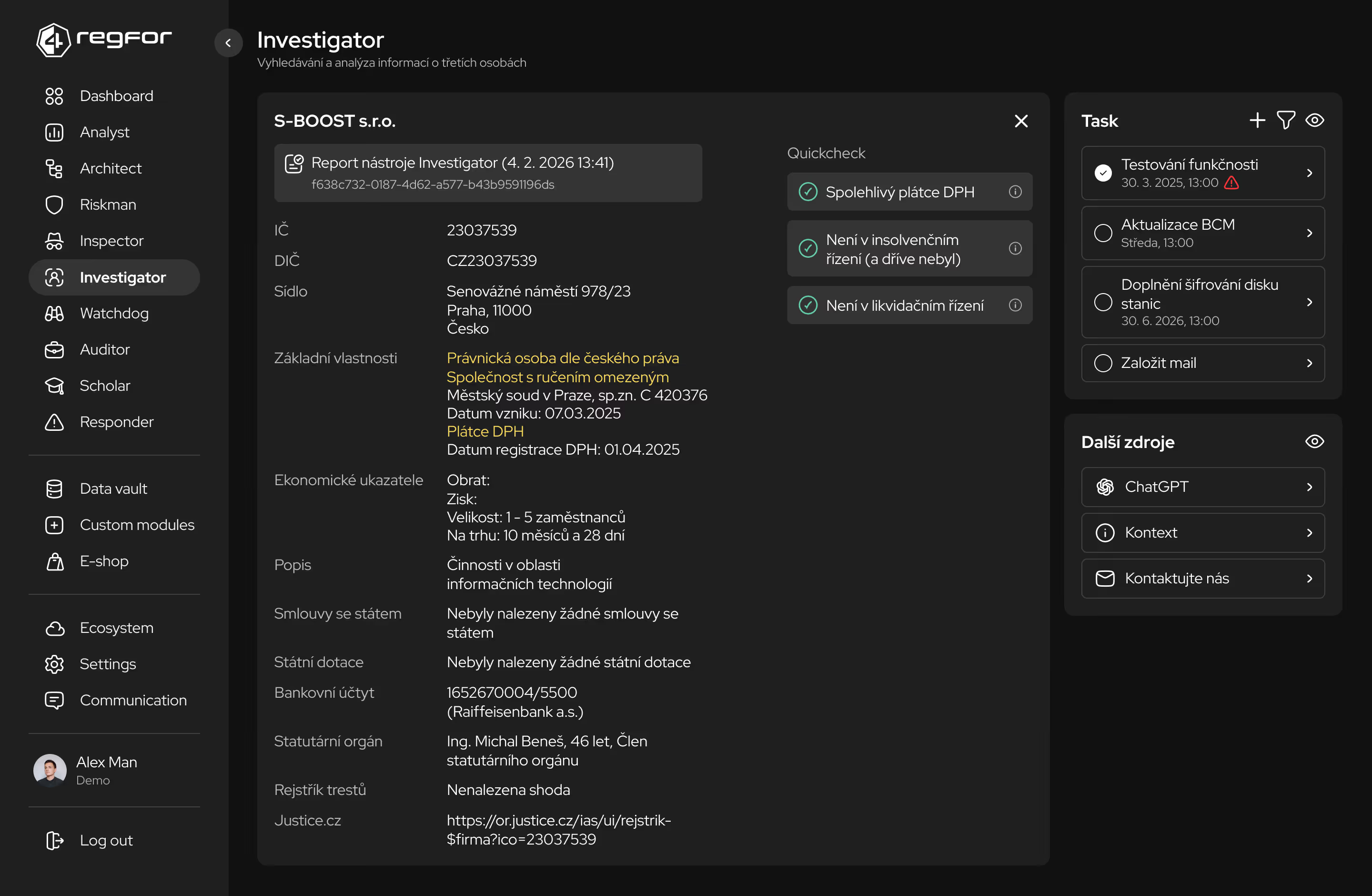
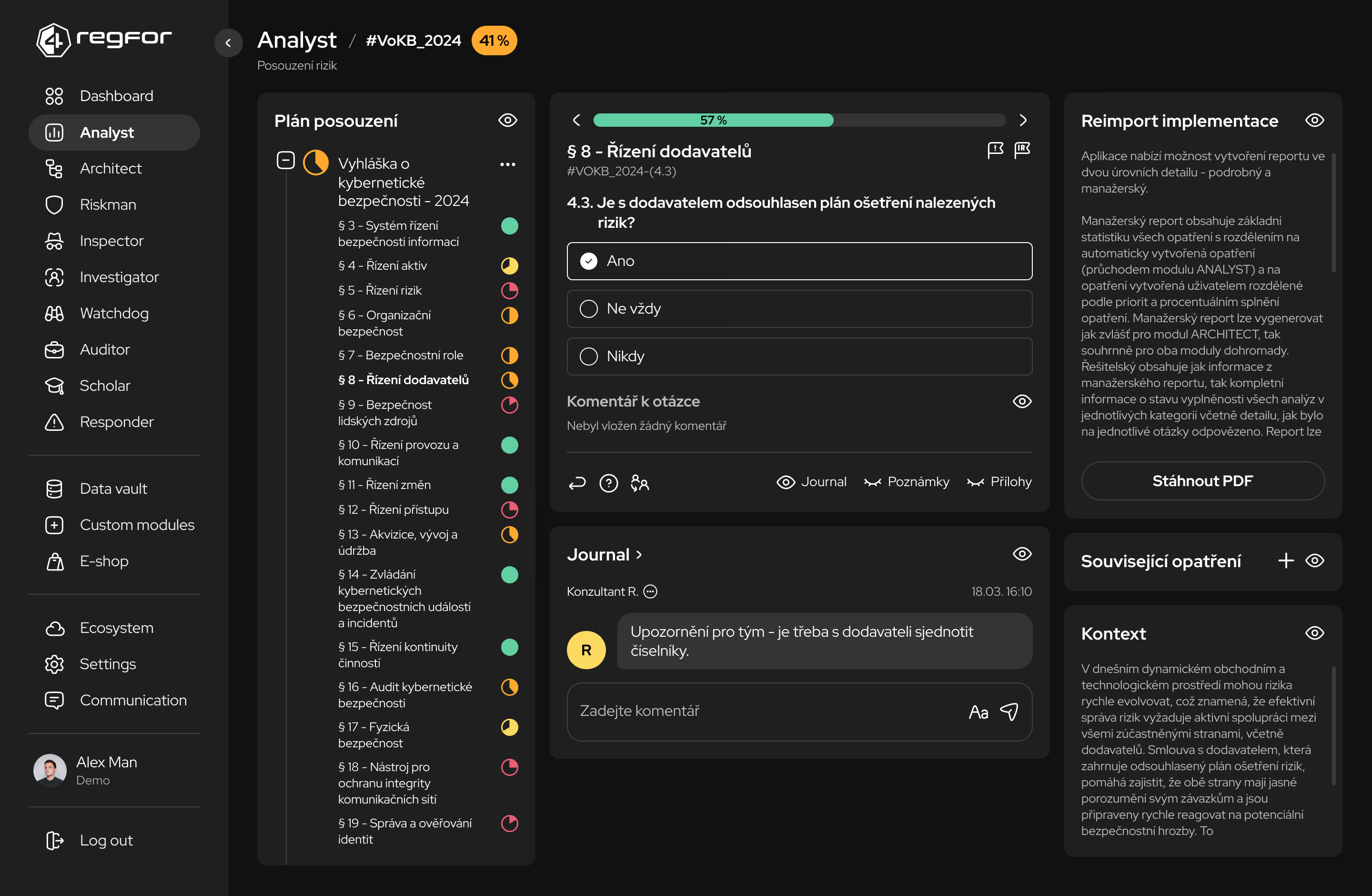
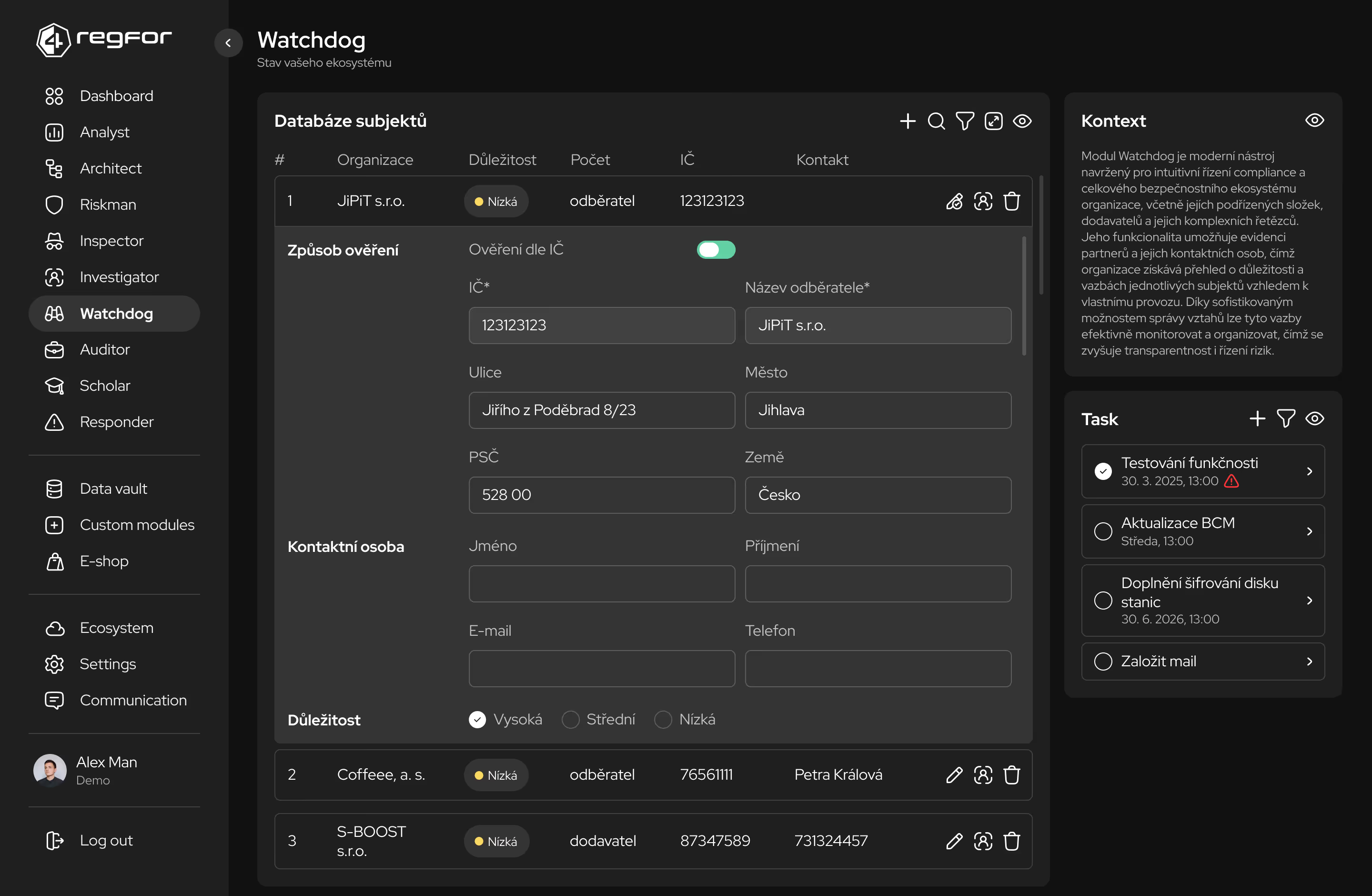
Systematická analýza požadavků z relevantních předpisů a jejich mapování na interní procesy organizace.
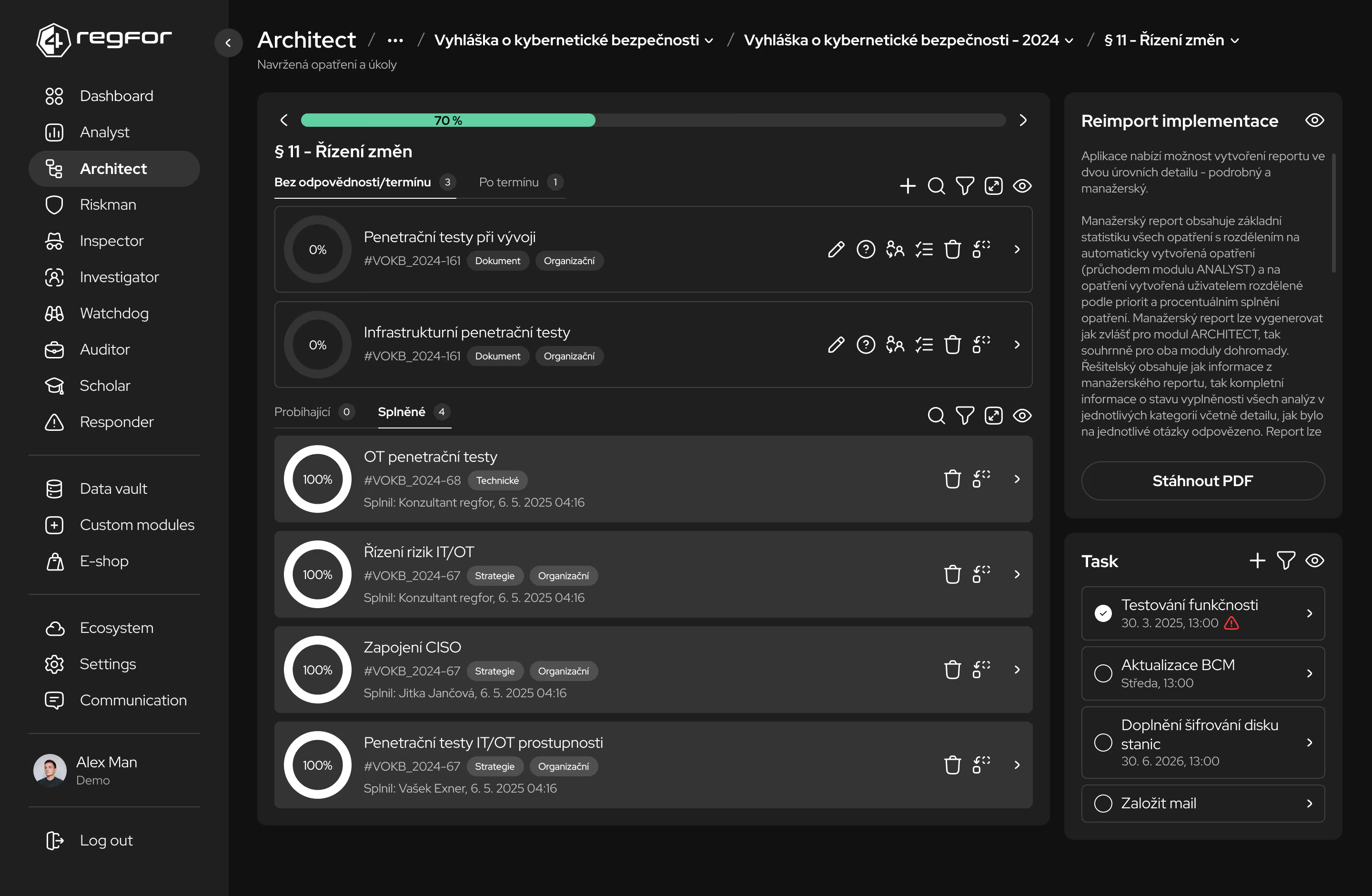
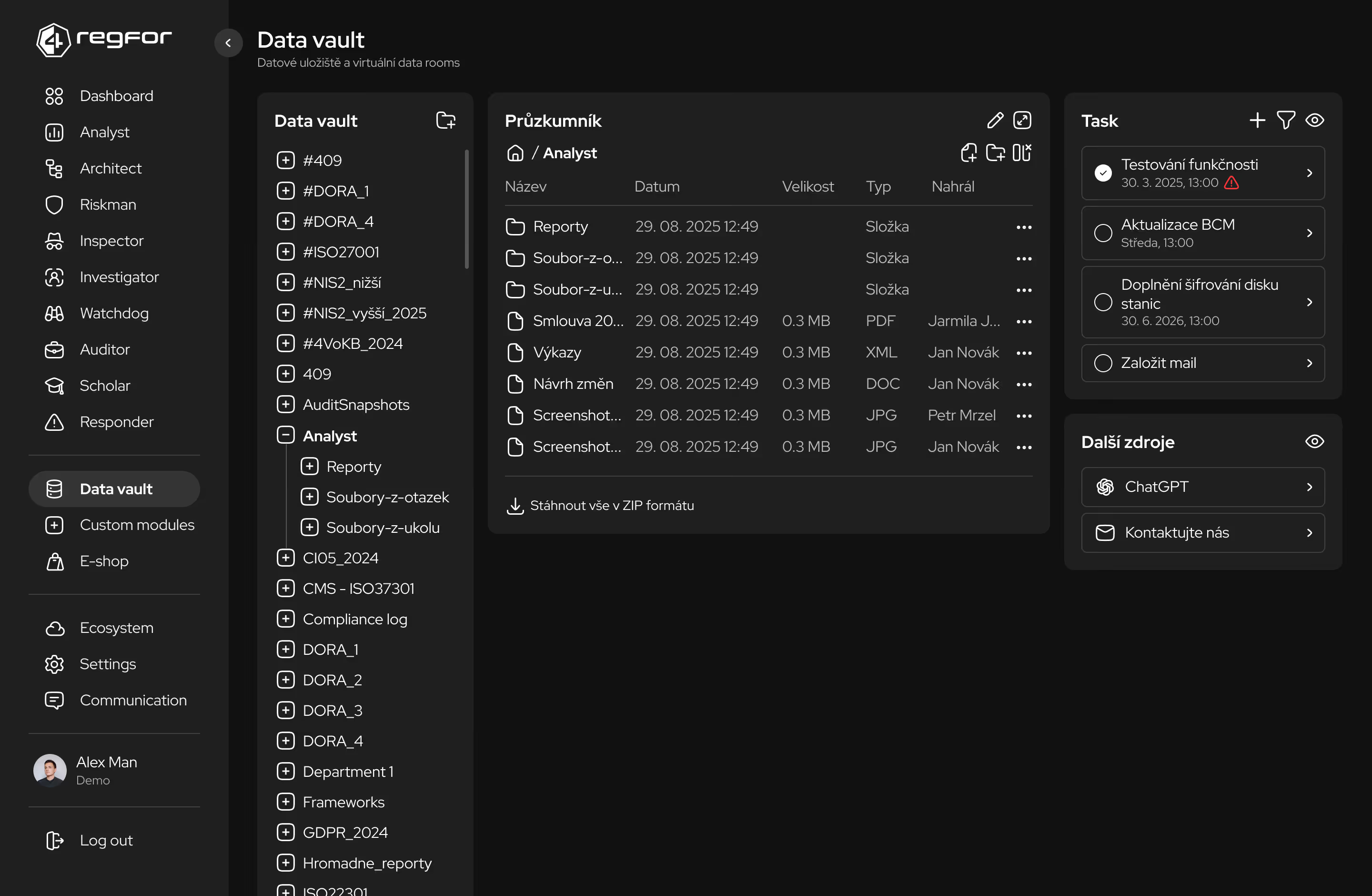
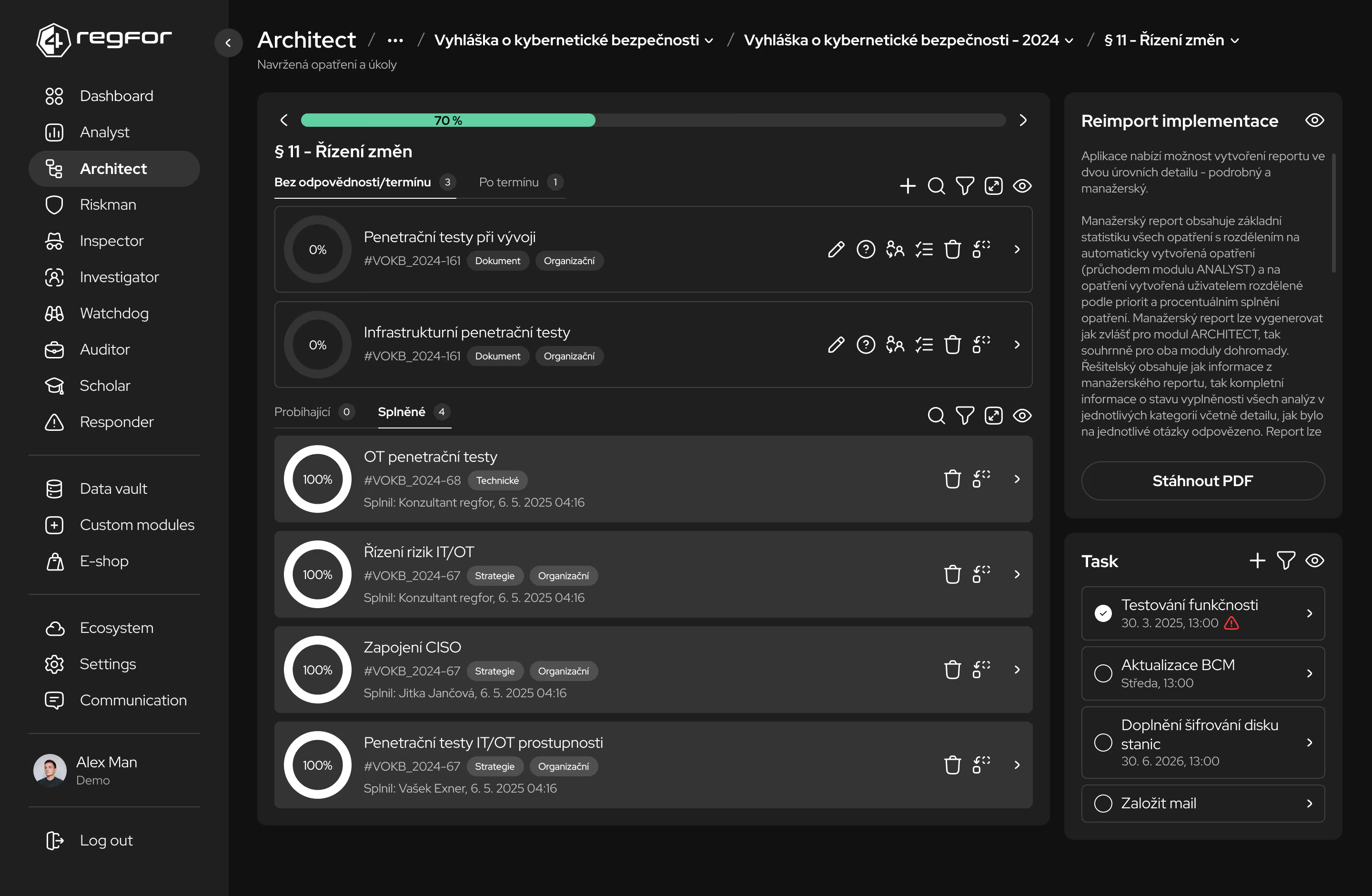
Centrální správa bezpečnostní dokumentace, politik a standardů s verzováním a schvalováním změn.
Automatizované sledování compliance stavu a identifikace oblastí vyžadujících pozornost.
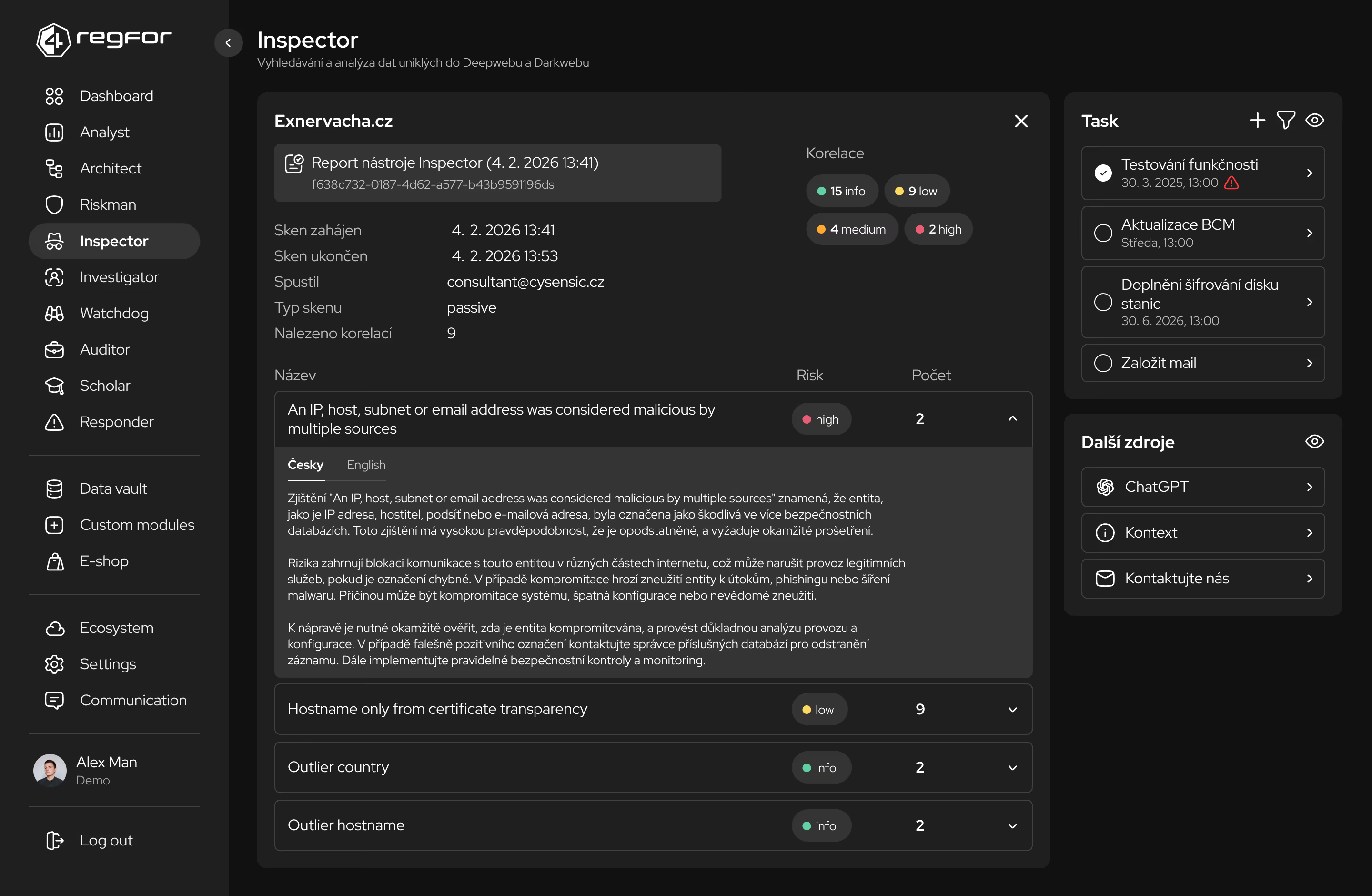
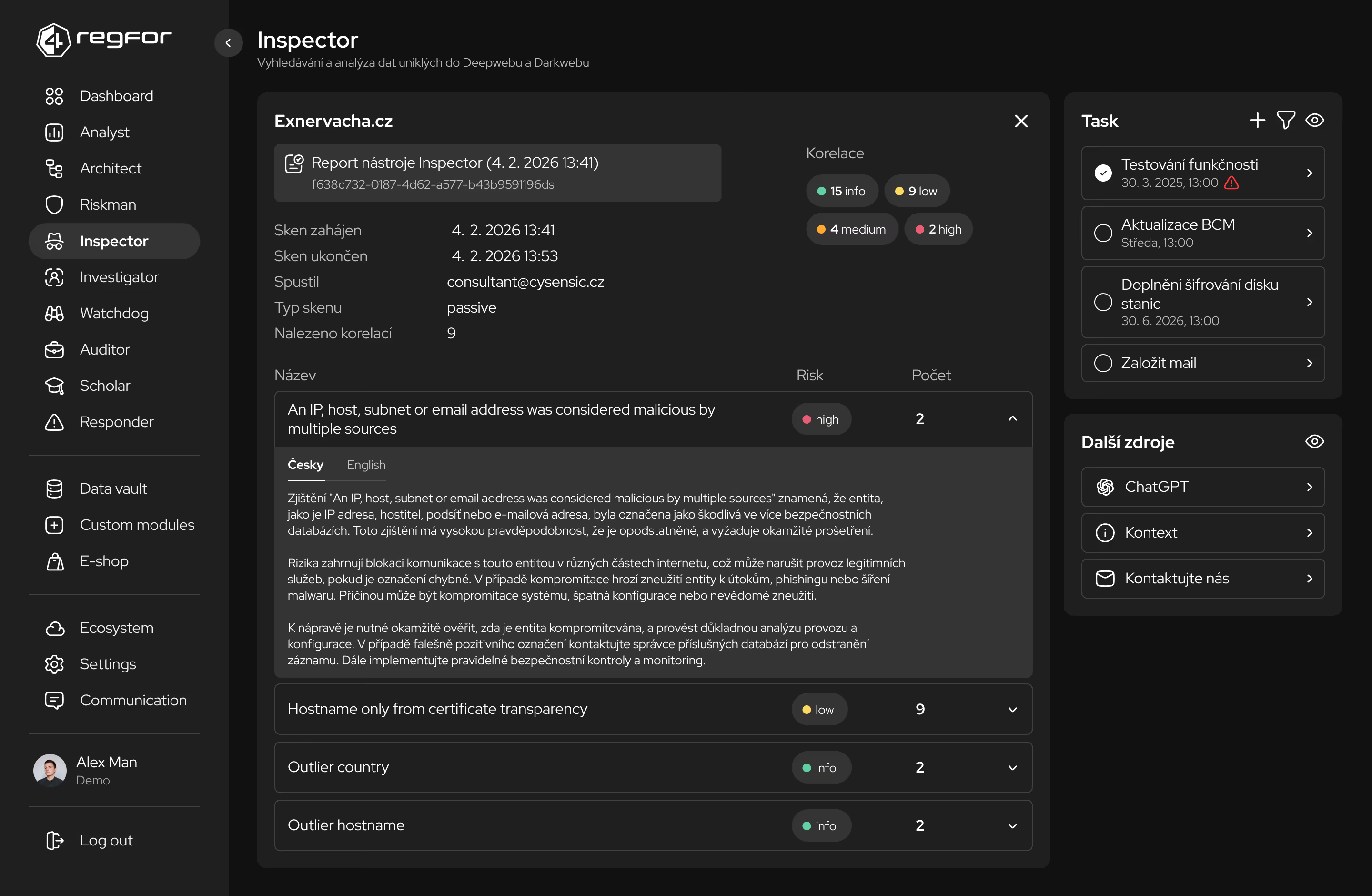
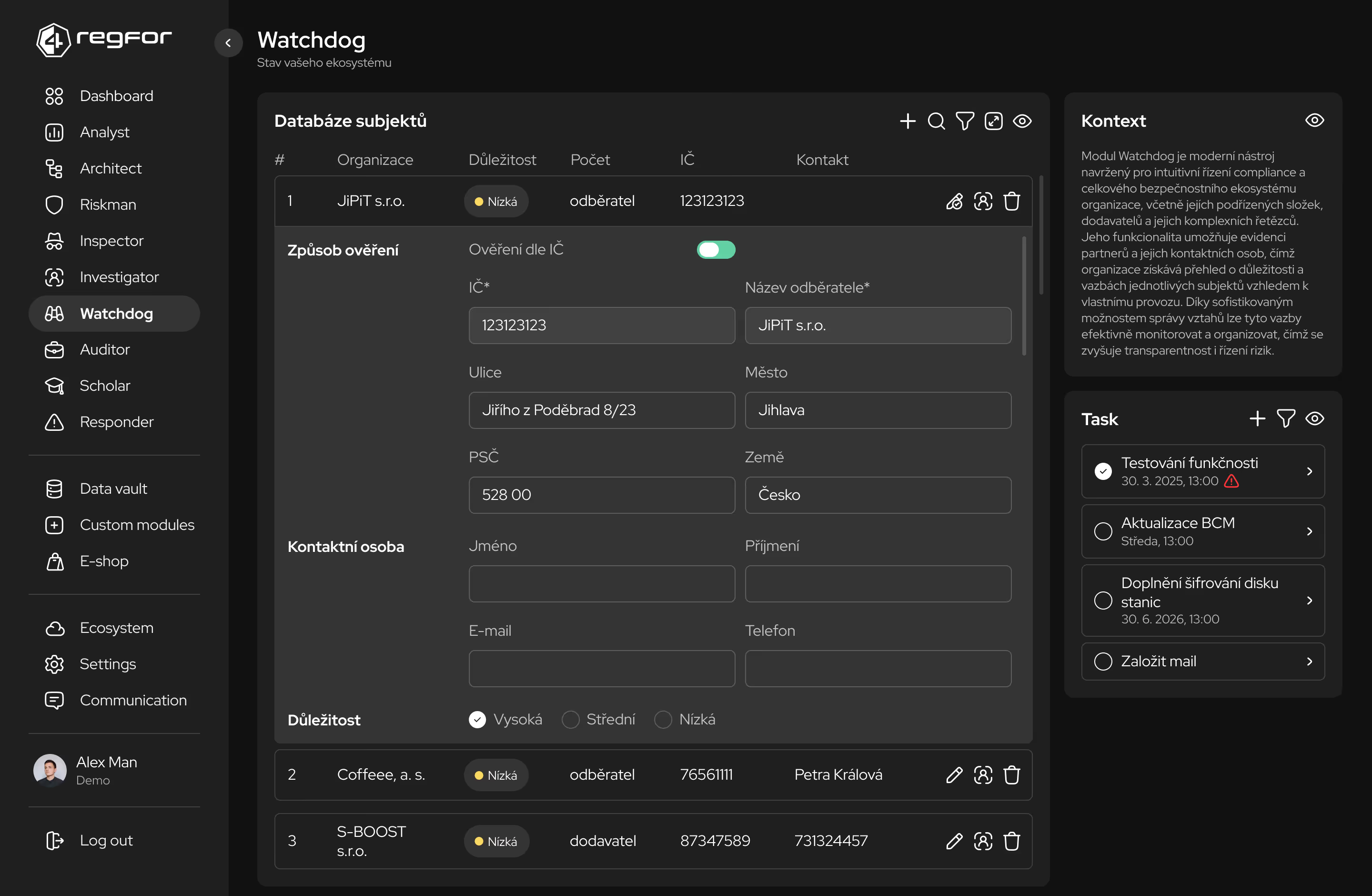
Kontinuální monitoring a detekce odchylek od stanovených bezpečnostních politik.
Řízení auditních procesů, kontrolních zjištění a nápravných opatření v jednom prostředí.
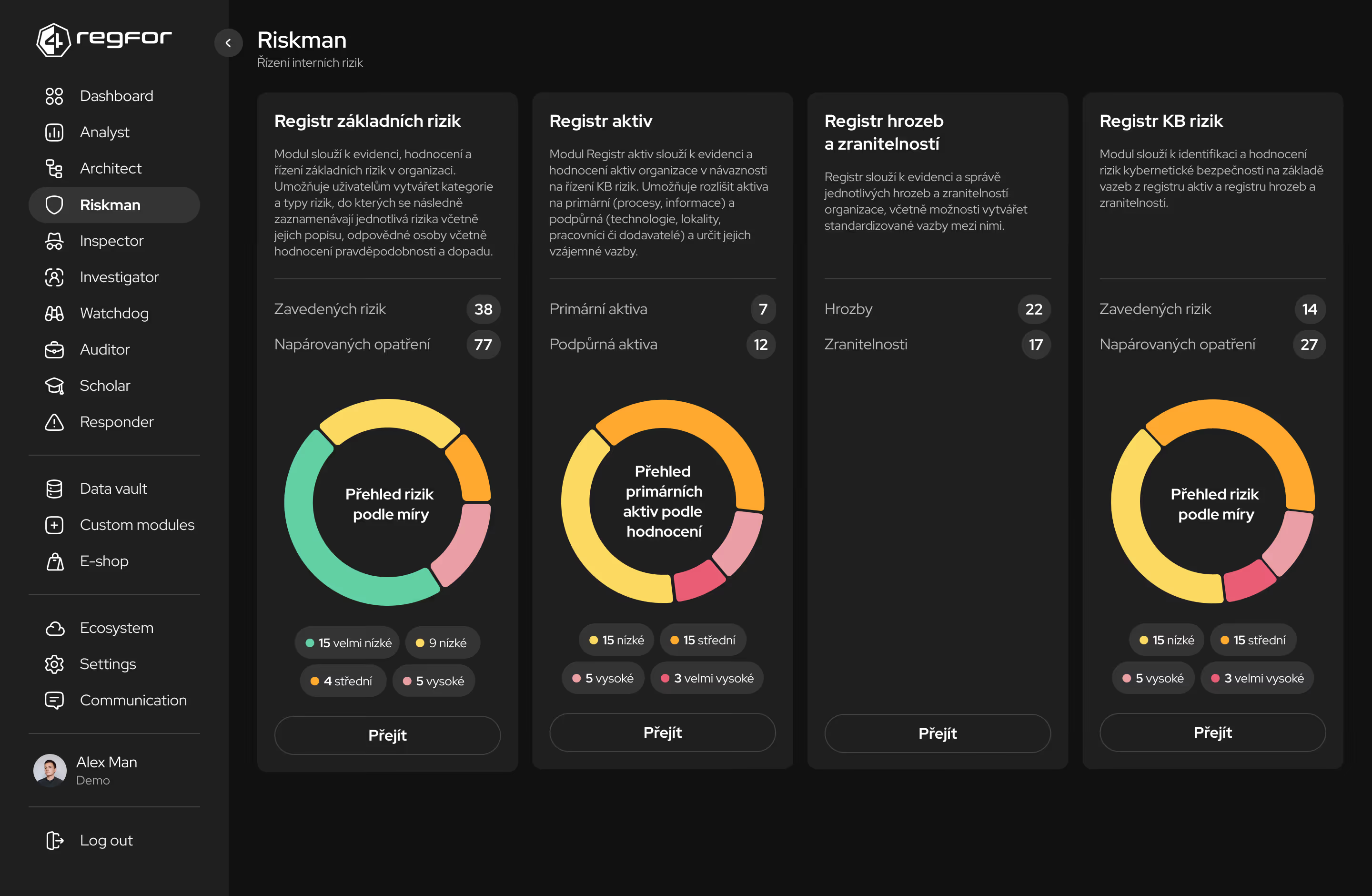
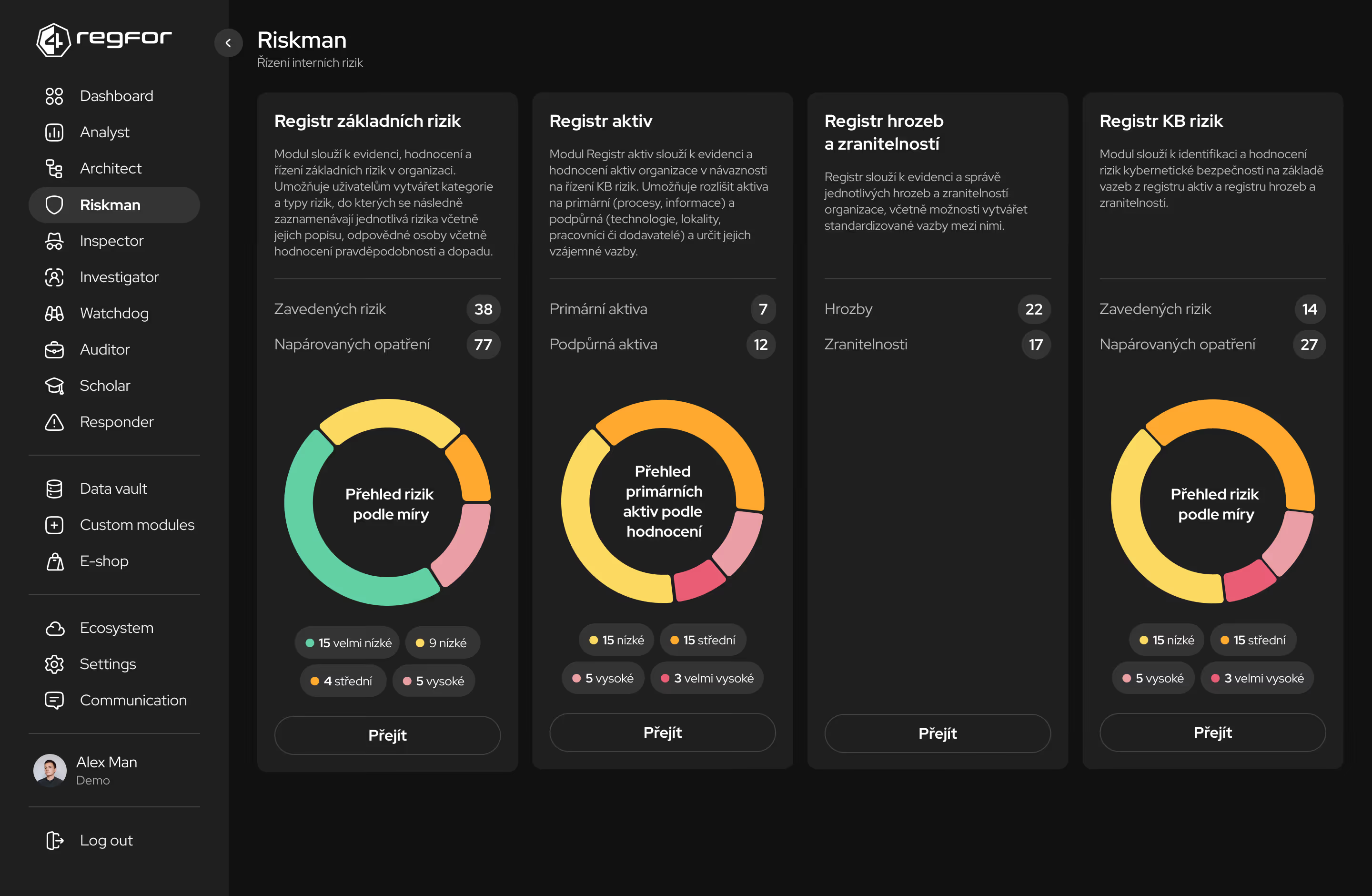
Komplexní správa rizik s metodickým rámcem pro identifikaci, hodnocení a mitigaci.
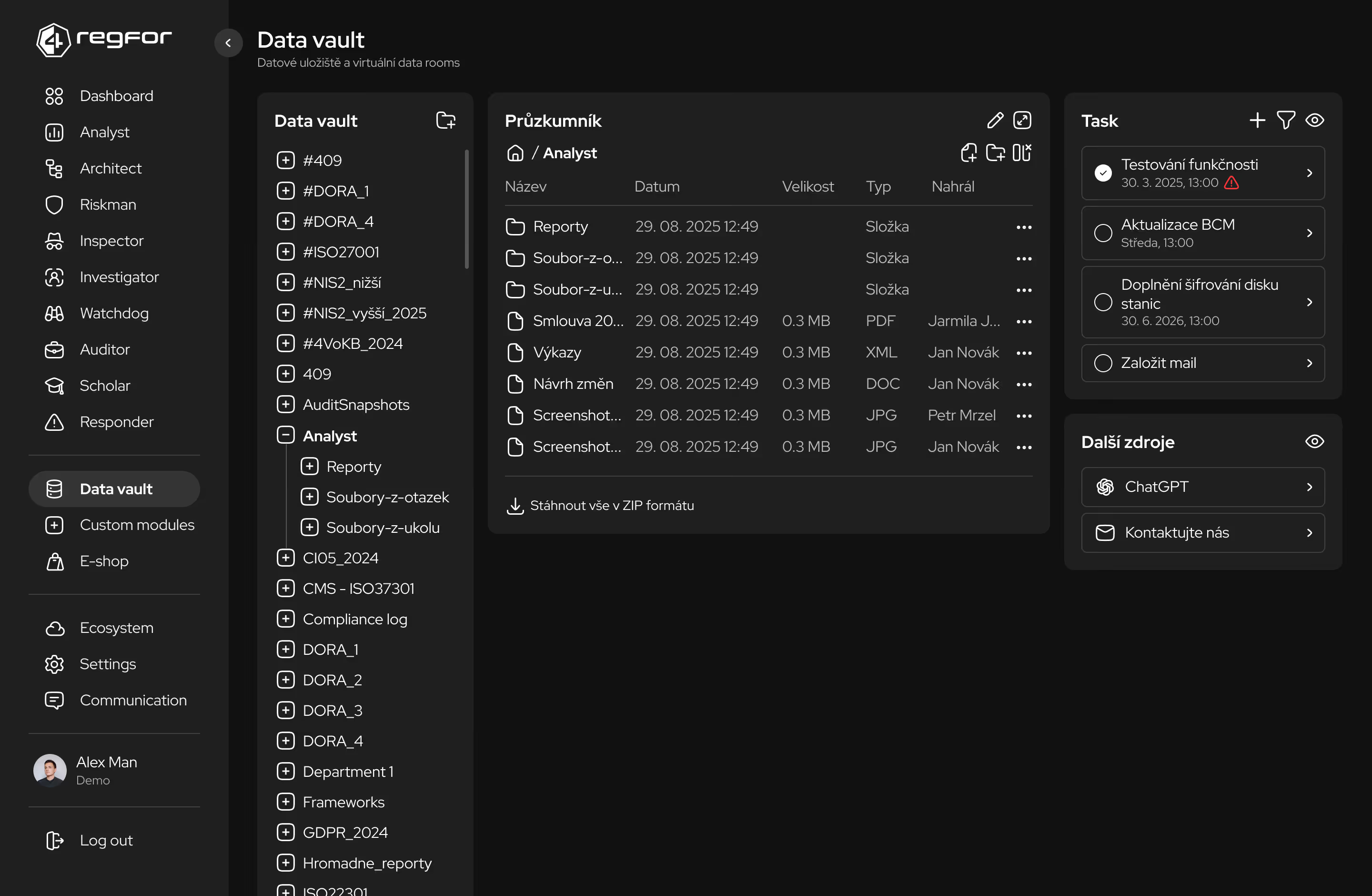
Bezpečné úložiště pro compliance dokumentaci s řízeným přístupem a auditním logem.